Ok it sounds like a sensational topic, but it’s actually true, it happened quite some time back (January), but I sat on it for some time to give them a chance to fix it.
Even though I believe in full disclosure, we have to be responsible to vendors and organisations too.
Basically it went down like this, I sent an E-mail to the editor of The Star[/url] about my feelings on the Malaysian Summons system and my post about it[/url].
He clicked on the link from a web based e-mail system and came to read the article, in doing so he passed a referal string to my site (This is a string holding the information of where you just came from, so if you came from a google search on donkeys I’ll get the referal string https://www.google.com.my/search?hl=en&q=donkeys&meta=).
So in the referal string I got from the web based e-mail page, contained the session ID for the Editor who was reading his mail, this session ID wasn’t cookie based, or machine based, it was just a Session ID, which enabled me to log straight into the Editors e-mail..
The referal string I got was something like this:
https://strmal.thestar.com.my/Xf3969c9b9d9b929c9a9e6012d8ab/rmail.41444.cgi?&mbx=MainXf3969c9b9d9b929c9a9e6012d8ab in this case is the session ID, simply by entering this link into my browser I could access the editors mail account, I tested and I could change everything except the password (as I don’t know the existing password) but by sending mail from this account I could probably social engineer the password to be changed.
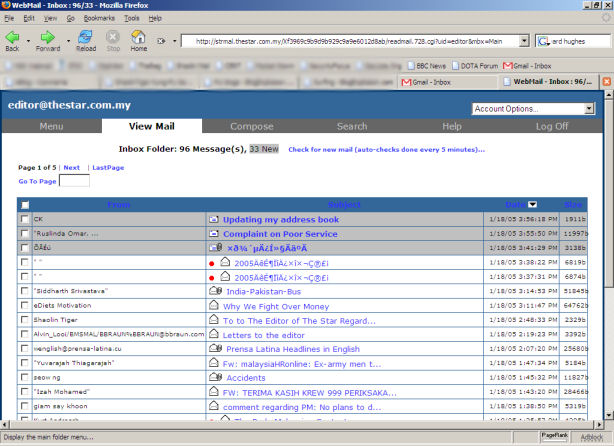
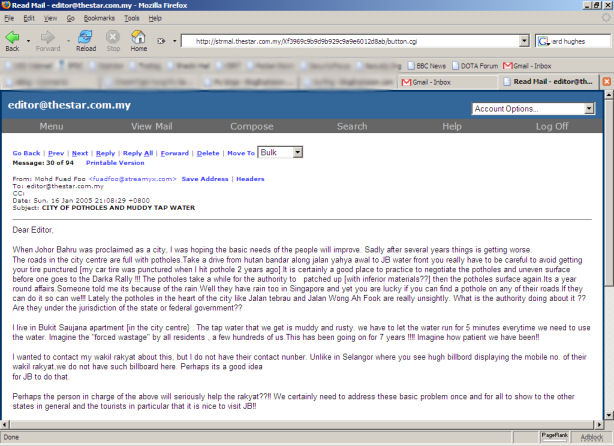
I could read all of the mail in the inbox and other folders
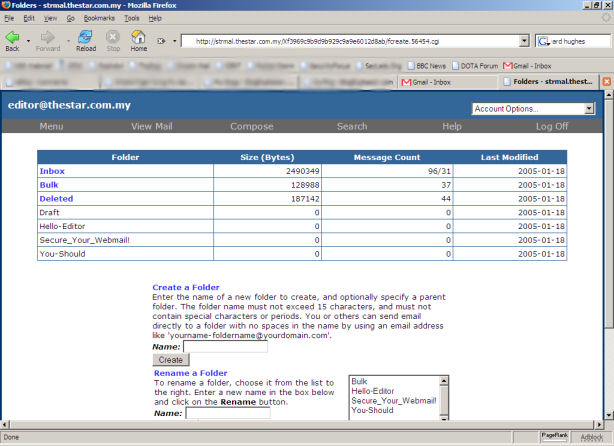
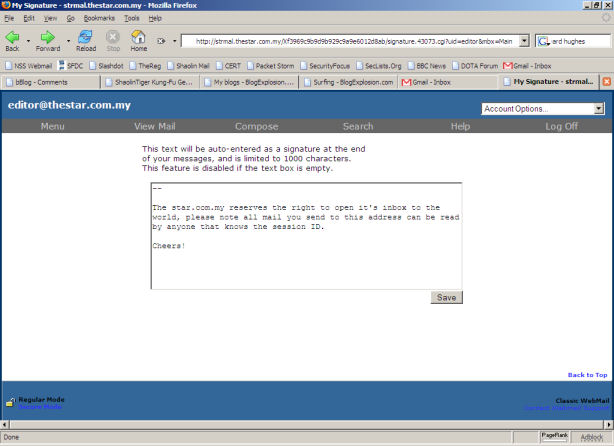
And change any settings I want..
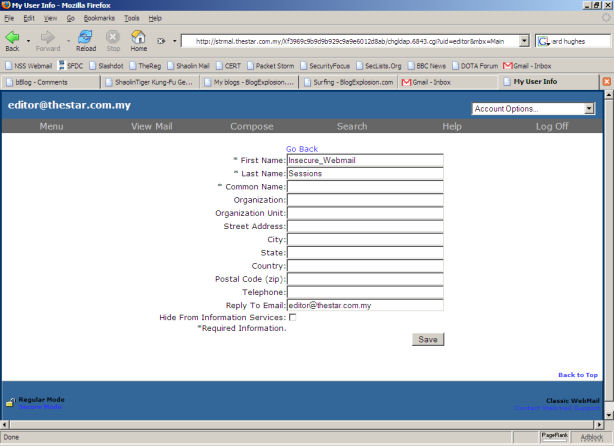
I ever gave them a more accurate signature:
If everyone is using this webmail system I could easily hijack their accounts too, this would be done by sending a HTML mail with a simple image imbedded inside, hosted on my domain, when the mail loaded it would load the image remotely (which your webmail allows I checked) and I would have the referer URL again in my weblogs with the relevant session ID.
Again I could just paste this into my browser and access the account of anyone using this webmail software.
It shows the current state of Information (in)Security in Malaysia.
I did of course e-mail them as soon as I found at and told them how to fix it.
This is just for your information.
On a similar note, if any of you have heard of The Global Malaysian Network[/url], again under the control of The Star[/url] was programmed insecurely.
The Global Malaysian Network is an initiative by The Star Malaysia (www.thestar.com.my) to facilitate networking and to tap into the resources, knowledge, skills, investment and contacts that Malaysians can offer to other Malaysians wherever they are in the world. The directory requires members to submit their personal details including their name, marital status, postal address, contact details, professional/occupation information and even educational background details.
Due to bad programming practices and unchecked variables there are several SQL injection vulnerabilities in the web application that powers the GM Directory. By manipulating the input strings a malicious attacker could potentially compromise the security of the database server and disclose any content within the database including private and sensitive information of the Directory members.
Owned by my friends over at Hack in the Box yesterday.
So The Star, I reckon you need to buck up your ideas when it comes to Infosec 🙂
bro, i still feel is not such a good idea posting this !!!!! serious …no matter how truthful or helpful you want to be. remember who runs the country.
dude, you should have told star the problem on the condition that they hire you as a consultant, like dogbert!
briliant! but better take care of yourself yah.
Lol!… pwned. They’re prolly pissin now.
deep …… lll …..
I guess the same trick wouldn’t work again….
I guess the same trick wouldn’t work again….by n30er.
of course it will, that’s why we have so many security flaws in malaysia.
should have tried bank negara instead.
YOU GEEEEEEK! YOU DA PWN!
… but won’t u get your ass into trouble for infringement of privacy or sumshits like that? I hope not!!!!!
It’s a helluva good way to send in yoru resume though. 😛
You damn ons. sexy ons.
Haha not really, look at it this way, if you left an important document face up on your desk and expected no one to read it, would that be realistic?
E-mail isn’t confidential anyway, it’s like a postcard, unless you encrypt it, any of the postmen (servers) along the way can read it.
Come let me hack you.
so damn geeky
Can I get a w00t w00t?!?
Dude you rawk.
yeah..right!..u rock!…wtf?…teach me woi!hhaaaa
Just FYI, this trick works on Yahoo as well.. 😀
hey.. found anything interesting in the editor mail box.. ??
good job…tiger
hey be nice la they’re excellent to hv beers with!
oiks..update la…19 today k
Good job, ST!
The state of information security in any largish organization can be frightening – it seems the larger they get, the more holes there are, even if they have an InfoSec cell.
A lot of times it seems to boil down to the organization having some “convenient service” in place that they want to keep, even once they’ve been audited. They ignore the advice of the contractors, only to end up 0Wn3D
You’d think people/companies would take IS more seriously, especially in this day and age – but 9/10 times they don’t. Scary…
Cheers,
Ted
OK, I seriously do not know if you wrote that post in English or Timbuktuan. But it sounds scary nontheless 🙂 So much for privacy huh?
As I have been telling everyone for years. The Internet is a library and not a place to store important or secret information. Its just old school news and the more they build on old platforms the worse it gets.
“If one man can make it, another can break it.”
Hahaha… U are da’man!!!
Maximum pwnage!
If it was evil me, I would have sent a few emails to me friends. Like, “congrats, you’ve been voted the sexiest blogger, and we’d like to interview you at Low Yat at 12 pm today.”
then, sit back and let the joy of maximum prankin’ wash over you
hai apa kabar awak adik itu kau sayang awak kau satu kini
khabar baik, tapi saya tak tau you nak cakap aper
haha this page also must have spy on our pc rite….
I don’t believe you..
not enought proof. show me more. 🙂
lolz, just a stupid mistake made by stupid web developer and discovered by nerd internet users. Nothing much special and should not say “hack”
lolz, just a stupid comment made by stupid ignorant fucker with no balls who posts anonymously and read by me. Nothing much special, should not say “comment” should say anal dribble.
ShaolinTiger, what do you think of owasp.org?